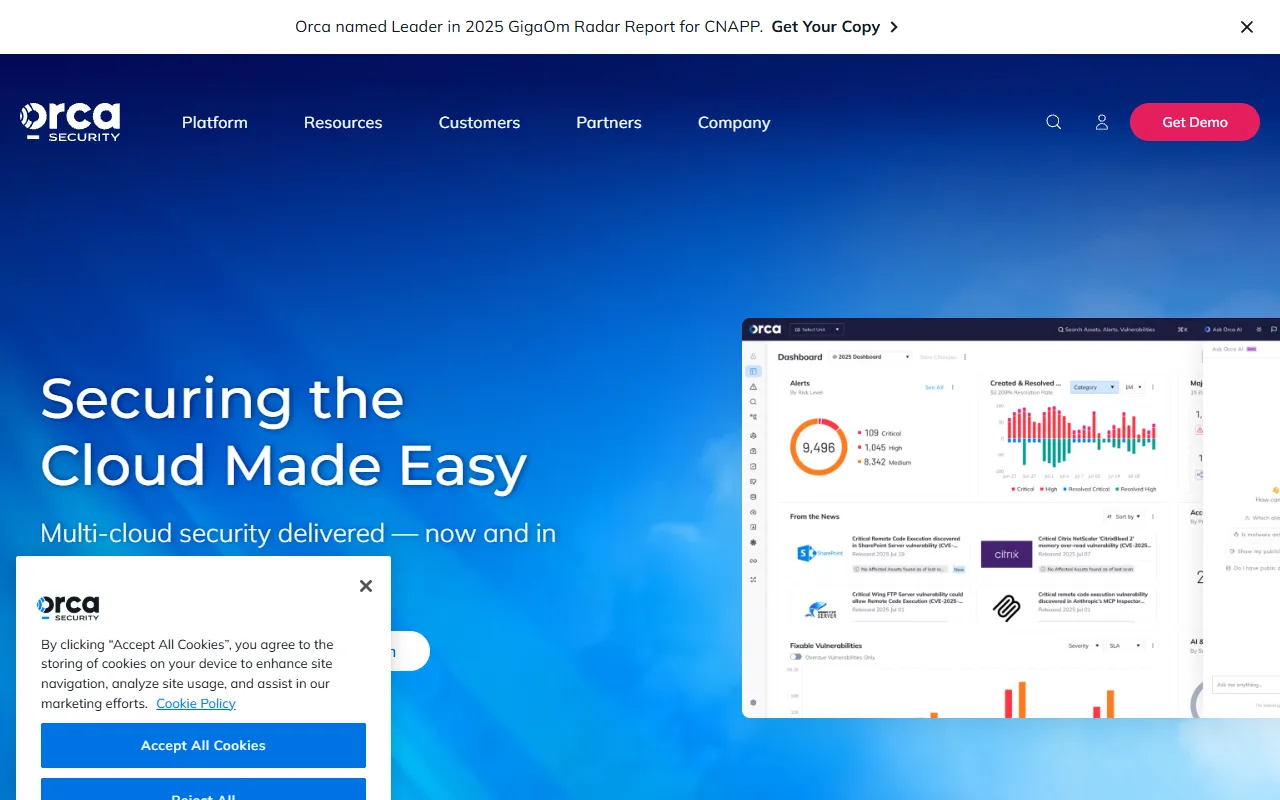
Orca Security
AI-powered cloud security platform that provides agentless visibility and risk prioritization.
Quick Take
AI-powered cloud security platform that provides agentless visibility and risk prioritization.
What We Like
- Strong integration options that connect with existing tools and workflows
- Responsive and modern design that works seamlessly across devices and screen sizes
- Consistent output quality that maintains professional standards across use cases
- Active development and regular updates suggest long-term viability and commitment
- Intuitive interface that balances power with accessibility for security engineers, IT teams, and compliance officers
What Could Be Better
- Internet connection required for AI processing and cloud-based features
- Results can vary depending on the quality and specificity of input provided
- Advanced features may take time to fully explore and master for optimal results
Pricing
PaidTool Overview
Tags
Orca Security enters the Cybersecurity AI arena as a purpose-built AI solution for security engineers, IT teams, and compliance officers. AI-powered cloud security platform that provides agentless visibility and risk prioritization. In a market crowded with generic tools, Orca Security distinguishes itself through its specialized focus on delivering measurable results in cybersecurity and risk management and a user experience designed to get you productive from day one.
This comprehensive review examines what Orca Security brings to the table, exploring its feature set, ideal use cases, pricing structure, and overall value proposition. Whether you are actively searching for a Cybersecurity AI solution or simply evaluating the landscape, this breakdown will help you determine if Orca Security deserves a spot in your toolkit.
Key Features of Orca Security
What makes Orca Security particularly interesting is its comprehensive feature set, which goes well beyond basic cybersecurity and threat detection functionality. Here is a closer look at what this tool brings to the table:
- Cloud security: Orca Security provides robust cloud security functionality, allowing users to protect with precision and efficiency. This feature is powered by advanced AI models that adapt to your specific use case and improve over time based on your interactions.
- CSPM: The cspm module in Orca Security is designed with real-world usage in mind, providing practical tools that integrate smoothly into existing workflows without disruption. Users can configure this feature to match their specific requirements.
- Vulnerability management: With built-in vulnerability management capabilities, Orca Security helps security engineers, IT teams, and compliance officers tackle this aspect of their workflow head-on. The AI-driven approach ensures consistent, high-quality output every time while reducing manual effort significantly.
- Agentless: Orca Security includes a dedicated agentless engine that processes your inputs intelligently. The system learns from each interaction, delivering increasingly personalized and accurate results the more you use it.
Taken together, these features paint a picture of a platform that takes cybersecurity and threat detection seriously. Each capability builds on the others, creating an integrated experience that is more than the sum of its parts.
How It Works
From the moment you open Orca Security, the workflow is designed to feel natural and efficient. The platform greets you with a clean, organized interface where your most common actions are immediately accessible. Whether you are starting a new project or continuing previous work, everything is just a click or two away, and the learning curve is minimal even for first-time users.
The AI powering Orca Security operates on cutting-edge models optimized for cybersecurity and threat detection. What this means in practice is that the tool does not just follow rigid rules; it understands the subtleties and variations inherent in cybersecurity and risk management. Inputs are analyzed contextually, and the generated output reflects an awareness of industry standards, best practices, and current trends.
Iteration is baked into how Orca Security works. After receiving initial results, users can fine-tune by adjusting settings, adding constraints, or simply asking for alternatives. This cycle of generation, review, and refinement mirrors how professionals naturally work, making the AI feel like a capable collaborator rather than a rigid automated system.
Beyond individual use, Orca Security supports integrations with the tools and platforms that security engineers, IT teams, and compliance officers already rely on. APIs, webhooks, and native integrations allow data to flow seamlessly between Orca Security and your broader technology ecosystem, eliminating the need for manual data transfers and keeping everything synchronized automatically.
Getting Started with Orca Security
Getting up and running with Orca Security is a straightforward process that takes just minutes. Start by visiting the platform and creating an account. Most users find that the onboarding wizard does an excellent job of configuring initial settings based on your role and goals, so you can skip the manual setup and jump straight into productive work. Visit the official website to create your account and explore the platform firsthand.
Once your account is set up, take a few minutes to explore the template library and preset configurations. These are designed to give you a head start by providing proven starting points for common tasks in cybersecurity and threat detection. From there, you can customize to your heart's content, but the templates ensure you are never staring at a blank screen wondering where to begin.
For teams looking to adopt Orca Security, the process is equally smooth. Administrator tools allow you to invite team members, set permissions, and establish shared resources in a centralized dashboard. The platform also provides documentation and tutorials that make self-service onboarding practical, reducing the burden on your internal training resources and accelerating time to value.
Best Suited For
While Orca Security casts a wide net, it truly shines for security engineers, IT teams, and compliance officers who are looking to enhance their output without sacrificing quality. If you find yourself spending too much time on repetitive tasks related to cybersecurity and threat detection, this tool could meaningfully change your workflow and free up hours each week for higher-value strategic work.
Beginners will benefit from the guided experience and templates that help them get started quickly, while experienced professionals will appreciate the depth of control and customization available beneath the surface. This dual-layer approach makes Orca Security accessible without being simplistic, catering to a wide spectrum of expertise levels.
Teams that collaborate frequently will also find significant value here, as Orca Security supports shared workflows that keep everyone aligned. The ability to establish consistent standards and share templates across a team ensures that quality remains high regardless of who is using the tool, making it an excellent choice for growing organizations.
Pricing Overview
Orca Security is a paid tool, which signals the team's commitment to delivering professional-grade capabilities and ongoing support. While the exact pricing may vary based on your selected plan and usage requirements, the investment is positioned to deliver clear ROI for security engineers, IT teams, and compliance officers who regularly work in cybersecurity and threat detection and need reliable, high-quality output.
When evaluating the cost, consider what you currently spend on alternative solutions, whether that is manual labor, freelancers, or competing tools. For many users, Orca Security pays for itself within the first month through time savings and improved output quality alone. The platform typically offers trial periods or money-back guarantees, so you can validate the value before making a long-term commitment.
Where Orca Security Fits in the Market
Understanding where Orca Security fits in the broader Cybersecurity AI ecosystem is important for making an informed decision. The market includes everything from lightweight utilities to comprehensive enterprise platforms, and Orca Security positions itself thoughtfully within this spectrum. Its strength lies in delivering focused cybersecurity and threat detection capabilities without the bloat and complexity that often accompany tools trying to do too many things at once.
What ultimately differentiates Orca Security from its competitors is the attention to workflow integration and user experience. Many tools in the cybersecurity and risk management space offer similar core capabilities on paper, but the execution, specifically how intuitive the interface feels and how seamlessly it fits into existing processes, is where Orca Security demonstrates genuine thoughtfulness. For security engineers, IT teams, and compliance officers evaluating multiple options, this practical usability factor often proves more important than raw feature counts.
The Bottom Line
After thorough evaluation, Orca Security stands out as a capable and thoughtfully designed tool in the Cybersecurity AI category. It addresses real pain points for security engineers, IT teams, and compliance officers without introducing unnecessary complexity, and the AI technology at its core delivers tangible improvements over manual approaches to cybersecurity and threat detection.
While it requires a financial investment, the returns in time savings and output quality make it a worthwhile consideration for serious security engineers, IT teams, and compliance officers who demand professional-grade results. In today's fast-moving landscape, having the right AI tools in your arsenal is increasingly becoming a competitive necessity rather than a luxury, and Orca Security makes a compelling case for inclusion.
Our verdict: Orca Security is worth your attention if you work in cybersecurity and risk management. The combination of smart features, accessible design, and genuine utility makes it a tool that earns its place through results rather than hype. Give it a try and judge the impact on your own workflow, as we believe you will be pleasantly surprised by what you find.
ADVERTISEMENT
728 x 90
Browse More Tools
View all
Connected Papers
Research ToolsVisual tool for exploring academic paper connections and building literature graphs.
Ironclad
Legal AIAI-powered contract lifecycle management platform for enterprise legal teams.
MindsDB
Data AnalyticsAI platform that brings machine learning directly into your existing databases.
AI Shirt Design Generator - YupTees
AI Image GenerationYupTees: AI-powered T-shirt design generator for fast, easy, and scalable print-on-demand creations.
Claude
AI AssistantsAnthropic's AI assistant known for thoughtful, nuanced responses, strong reasoning capabilities, and a focus on safety and helpfulness.
AlphaFold
Science AIDeepMind AI system that predicts 3D protein structures with remarkable accuracy.
Cursor
Code AssistantsAn AI-first code editor built on VS Code that integrates AI deeply into every aspect of the coding experience, from writing to debugging.
ChatGPT
AI AssistantsOpenAI's conversational AI assistant capable of generating text, answering questions, writing code, and assisting with a wide range of tasks.
Claid.ai
Image EditingAI product photo editing with automated background removal, upscaling, and enhancement.